Video at a glance
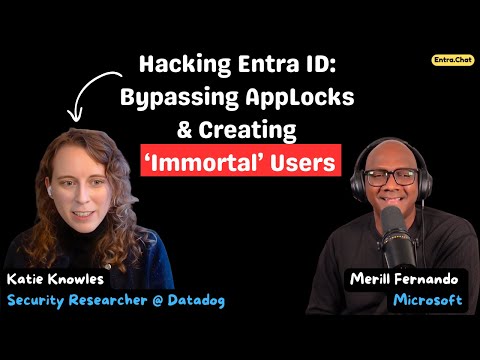
In a recent YouTube interview produced by Merill Fernando, security researcher Katie Knowles walks viewers through hidden risks inside Microsoft Entra. The conversation exposes practical attack paths such as backdooring service principals, a bug in restricted administrative units that can create undeletable accounts, and clever OAuth phishing using Copilot Studio. Moreover, the interview blends technical detail with defensive guidance so listeners can translate findings into real-world controls. Consequently, this episode serves as both a primer and a call to action for identity defenders and IT leaders.
What researchers uncovered
First, Knowles demonstrates how attackers can manipulate application identities to gain persistent access, effectively backdooring service principals so they survive routine cleanups. Next, she explains the so-called "immortal user" bug in restricted administrative units, where a misconfiguration or platform bug prevents deletion of a malicious account, increasing attacker dwell time. In addition, the interview highlights an elegant phishing technique that uses Copilot Studio as a wrapper for credential-stealing OAuth flows, which can fool both users and automated controls into granting access.
Then, Knowles details how defenders can overlook gaps such as bypasses to AppLock and risky Azure settings like overly permissive Azure Key Vault access policies that expand an attack surface unexpectedly. She also clarifies the difference between app registrations and service principals, outlining how identity artifacts move through lifecycle states and where trust boundaries blur. Finally, the discussion touches on future risks tied to emerging concepts like Agent IDs and an evolving trust model that will change how organizations authenticate non-human agents.
AI-driven changes in Entra and what they mean
During the same episode, the conversation shifts to recent 2025 updates that embed AI into identity workflows, such as Security Copilot and the Conditional Access Optimization Agent. These tools promise faster threat detection and continuous tuning of access policies, reducing manual toil while surfacing anomalous tokens, impossible travel, and unfamiliar sign-ins more reliably. Moreover, Microsoft’s push toward passwordless sign-in options and certificate-based app authentication aims to modernize identity hygiene across devices and services.
However, Knowles points out that AI-driven automation brings tradeoffs; while machine learning can lower false positives, it can also obscure why a decision occurred unless telemetry and explainability improve. Consequently, security teams must balance reliance on intelligent agents with human review processes to avoid blind spots. In short, AI can accelerate defenses, but only if organizations invest in observability and governance that make automated decisions auditable and reversible.
Tradeoffs and operational challenges
One major tradeoff centers on usability versus security: tighter controls like forced MFA, stricter app governance, and token revocation reduce risk but increase friction for developers and users, which can lead to shadow IT or risky workarounds. Furthermore, the increasing number of identity primitives—app registrations, service principals, managed identities, and agent IDs—creates complexity that defenders must track or else risk stale entitlements. Therefore, teams must choose where to accept complexity and where to simplify processes to maintain both security and productivity.
Another challenge is resource allocation: continuous policy tuning and AI monitoring require skilled personnel and good signal data, while small teams may struggle to validate false positives, debug automation, or triage nuanced identity incidents. Moreover, platform bugs like the immutable account issue show that even well-configured tenants can be vulnerable to systemic failures, which complicates incident response and recovery. Consequently, organizations should prepare playbooks that combine technical fixes with governance decisions and vendor coordination.
Practical guidance and closing thoughts
Knowles’ recommendations, as presented by Merill Fernando, emphasize proactive app governance, regular auditing of administrative units, and simulation of OAuth flows to detect weak points before attackers do. In addition, teams should log and monitor app consent events, review key vault policies regularly, and verify that automated agents and AI-driven policy changes are both transparent and reversible. By contrast, neglecting these basics invites attacker persistence and makes remediation slow and costly.
In conclusion, the video offers a clear message: identity security in Microsoft Entra is improving through AI and automation, but it is also growing more complex, which raises fresh risks and operational tradeoffs. Therefore, organizations should pair new platform capabilities with strong governance, observability, and periodic red-team-style testing to keep pace. Overall, Merill Fernando’s interview with Katie Knowles is a useful resource for anyone responsible for identity and access management who wants to think differently about modern identity threats.