
Microsoft Entra: Before You Trust, Watch This Guide!
Maximize Security & Trust with Microsoft Entras Two-Way Trust Feature: How to Setup & Validate!
Key insights
- Create a one-way outbound trust from Microsoft Entra Domain Services to on-premises AD DS environments to facilitate authentication and resource access.
- Configure DNS in an on-premises AD DS environment to support Domain Services connectivity and create both inbound and outbound forest trusts.
- Ensure continuous network connectivity and name resolution between your Domain Services forest and your on-premises Active Directory forest.
- Validate resource authentication by testing user authentication from the Domain Services forest and accessing resources using on-premises user credentials.
- For environments that no longer need the forest trust, follow steps to remove the trust from both the Domain Services and the on-premises domain.
Microsoft Entra and Forest Trusts
Microsoft Entra is a powerful tool for managing identities and access across a range of environments, including cloud and on-premises setups. It's designed to facilitate secure and seamless authentication, allowing for a more integrated IT ecosystem. The introduction of forest trusts within Microsoft Entra's domain services, particularly the new two-way trust feature, marks a significant enhancement in how resources and user credentials are managed and authenticated across different domains.
Forest trusts enable organizations to extend access to resources across distinct, independent directories, bridging the gap between cloud-based services and on-premises Active Directory domains. This is particularly valuable in hybrid environments where organizations aim to leverage the cloud's scalability and accessibility while maintaining on-premises systems for certain operations or requirements. By doing so, users can enjoy seamless access to resources regardless of where they are hosted, without compromising on security.
The setup process involves configuring DNS settings to ensure connectivity between different domains, creating the appropriate trust relationships, and ensuring continuous network connectivity for a stable user experience. Additionally, testing and validation steps are crucial to confirm that the trust relationship facilitates proper authentication and resource access as intended.
This integration represents a step forward in addressing the complexities associated with managing identities and access in hybrid and multi-cloud environments. With Microsoft Entra and forest trusts, organizations can now achieve more cohesive and secure management of user identities and access permissions, ensuring that only authorized users can access sensitive resources, regardless of where these resources reside.
Wondering if you can trust Microsoft Entra? A new video by Azure Academy dives deep into the setup of the 2 Way Trust feature in Microsoft Entra Domain Services. It's a tutorial on creating a forest trust in an on-premises domain, ensuring strong security and trustworthiness.
You can establish a one-way outbound trust from Microsoft Entra Domain Services to on-premises AD DS environments. This feature is crucial for users, applications, and computers that authenticate against an on-premises domain. It's beneficial in environments requiring smart card logins or in hybrid scenarios needing access to on-premises domains.
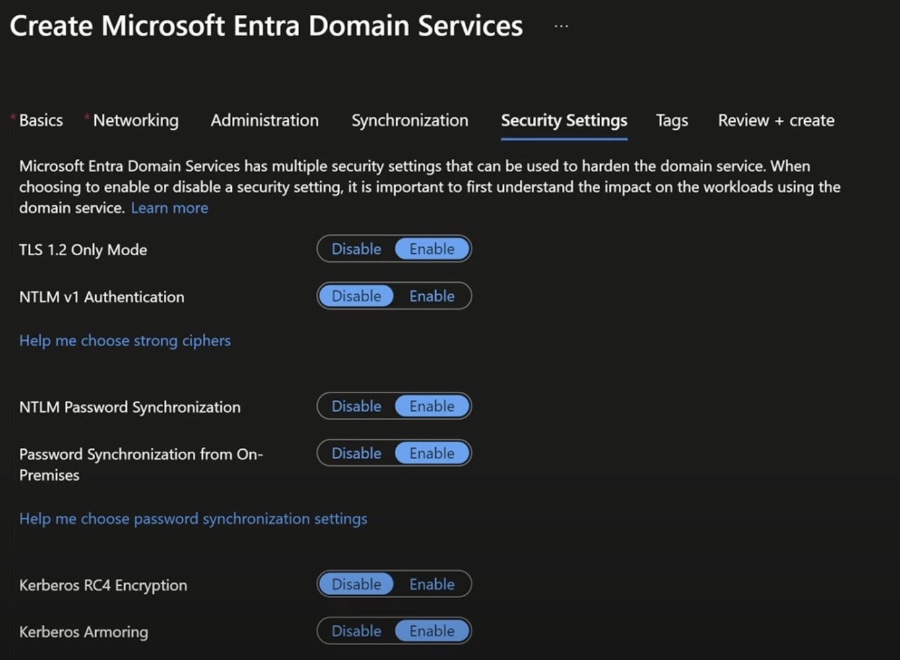
The tutorial explains creating an outbound forest trust, highlighting the prevention of UPN collisions through automatic synchronization blocking. The process involves configuring DNS in on-premises environments for connectivity, creating both inbound and outbound forest trusts, and testing the trust relationship for authentication and resource access.
To begin, you need an active Azure subscription and a Microsoft Entra tenant. The tutorial emphasizes the importance of having a stable network connection between the Azure virtual network and the on-premises Active Directory to avoid authentication issues or resource access failures.
Proper DNS configuration in the on-premises domain is crucial. Steps include setting up conditional forwarders in the existing DNS servers. This setup ensures that the managed domain is correctly resolved from the on-premises environment, a vital step for creating the necessary trust.
The process of creating an inbound forest trust in the on-premises domain and an outbound forest trust in Domain Services is meticulously guided. It includes detailed steps to complete these tasks from a management workstation and through the Microsoft Entra admin center, ensuring a secure and seamless trust relationship setup.
Key activities such as enabling file and printer sharing, creating a security group and adding members, and validating cross-forest authentication to resources are covered. These examples demonstrate practical application scenarios, illustrating the importance of proper setup and configuration for efficient resource access.
The tutorial concludes with steps for validating cross-forest authentication, ensuring that users from the on-premises domain can access resources in the Domain Services forest. Detailed instructions for testing file sharing, user authentication, and permissions validation are provided.
For those interested in further securing their network and ensuring seamless integration between cloud and on-premises environments, the tutorial offers valuable insights and detailed instructions. It encapsulates the essence of establishing and managing trust relationships within Microsoft Entra Domain Services, providing a cornerstone for secure, authenticated access to resources in hybrid scenarios.

People also ask
"Why did Microsoft change Azure to Entra?"
The renaming of Azure to Microsoft Entra more effectively conveys the product's ability to support a variety of cloud platforms and environments. This change addresses any potential confusion with Azure's on-premises counterpart, Active Directory, by presenting a clearer distinction. Additionally, it lays the groundwork for enhancing the approach to safeguarding all identities and fortifying the protection across all access points as the service continues to evolve and broaden its capabilities.
"How does Microsoft Entra work?"
Microsoft Entra enhances security by safeguarding user identities and streamlining the login process. It introduces convenient functionalities like self-service password reset, which empowers users to modify or recuperate their passwords through a web interface accessible from any device. This is particularly advantageous for users who have either forgotten their passwords or find their accounts temporarily inaccessible.
Keywords
Microsoft Entra, Trust, Security, Identity Management, Access Control, Cybersecurity, Cloud Security, Authentication