
Microsoft Defender Identity Full Demo Guide 2023
Microsoft 365 Expert, Author, YouTuber, Speaker & Senior Technology Instructor (MCT)
Maximize Your Cybersecurity Strategy with Microsoft Defender for Identity: Discover Cutting-Edge AI Threat Prevention Techniques!
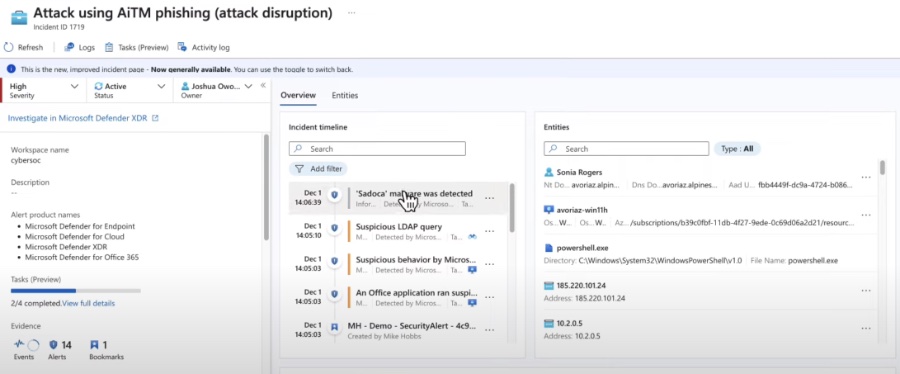
Join us as we explore Microsoft Defender for Identity in this comprehensive episode featuring a full demonstration. Learn the setup and configuration process that can bolster your cybersecurity measures. Additionally, witness how to combat Advisory In the Middle Attacks (AiTM) using Microsoft's advanced XDR platform.
Leverage the power of artificial intelligence and machine learning to analyze user behaviors and secure login attempts. Whether you're seeking certification or aiming to expand your knowledge, this session is filled with valuable demonstrations. Watch and learn how these tools can enhance your organization's protection against cyber threats.
Microsoft Defender for Identity
Microsoft Defender for Identity is highlighted as a crucial tool for securing infrastructure against cyber threats. Specifically, the video provides a thorough demonstration of setting up and configuring Defender for Identity. It also showcases how the tool tackles Advisory In the Middle Attack (AiTM).
With the integration of AI and machine learning, Defender for Identity analyses user behaviour constantly. This analysis helps in the early detection of suspicious login attempts or activities. The video is very informative, particularly for those seeking certification or who simply wish to enhance their understanding of the solution.
Defender for Identity is described as a cloud-based security solution. Its role is to help organizations prevent advanced cyber attacks and insider threats in hybrid environments. The solution allows enterprises to detect, investigate, and react to threats swiftly and effectively.
Key features of Microsoft Defender for Identity:
- Continuous monitoring of identity activity
- Advanced threat detection
- Integrated investigation and response
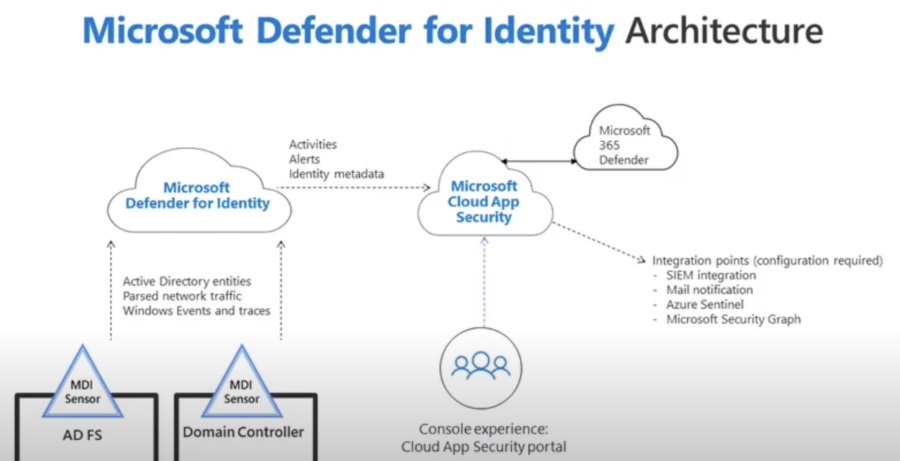
- Integration with Microsoft Defender for Cloud Apps
These features collectively empower organizations to keep a vigilant eye on identity-related activities. These activities encompass user logins, password changes, and access to sensitive data across both on-premise and cloud-based environments.
The video also explores the tangible benefits of deploying Defender for Identity. These benefits include minimized risk of identity-based attacks, enhanced security posture, and reduced costs related to security incidents.
Benefits of using Microsoft Defender for Identity:
- Reduced risk of identity-based attacks
- Improved security posture
- Reduced costs
Looking at specific use-cases, organizations at high risk of targeted attacks or with many remote users can reap the most benefits. Furthermore, those in highly regulated industries may find Defender for Identity crucial to meeting compliance demands.
Who should use Microsoft Defender for Identity:
- Organizations at high risk of targeted attacks
- Organizations with a large number of remote users
- Organizations in highly regulated industries
Microsoft Defender for Identity is a security service designed for hybrid environments, offering protection against cyber attacks and insider threats. It provides non-stop monitoring of identity activities, allowing for prompt detection, investigation, and response to potential threats. Experience effective security management and threat mitigation with Defender for Identity.
Continuous monitoring of all identity activity is a core feature, tracking events across Active Directory and cloud services. Advanced threat detection employs machine learning to identify suspicious behaviors, flagging potential attacks. Microsoft's Defender for Identity eases the investigation and response process through an integrated portal with comprehensive tools.
Integrate Microsoft Defender for Identity with Microsoft Defender for Cloud Apps for a full view of identity and application security. Lower the risk of attacks targeting your identity infrastructure, enhancing your overall security stance. Plus, enjoy cost reductions associated with managing and mitigating security threats efficiently.
Organizations using Active Directory and cloud-based identity providers should consider implementing Microsoft Defender for Identity. It is particularly beneficial for those facing a high risk of targeted cyber attacks or having a significant number of users working remotely. Compliance-driven industries can also find this tool valuable for meeting regulatory standards.
With Microsoft Defender for Identity, you can help your security team handle identity risks and detect sophisticated cyber threats. Understanding your identity landscape is essential to minimizing exposure to these attacks. Monitor your cyber threats in real time with alerts designed to detect common and emerging attack patterns.
Further Exploration into Microsoft Defender for Identity
Microsoft Defender for Identity serves as an essential component in building a robust cybersecurity framework. It focuses on protecting against cyber threats that target user identities, which are often the weakest link in security chains. With the increasing complexity of cyber attacks, organizations need to be proactive in monitoring, detecting, and responding to potential threats to their identity infrastructures.
Working in tandem with other Microsoft security tools, Defender for Identity offers a comprehensive defense strategy that includes real-time threat detection, advanced analytics, and integrated response mechanisms. It stands out as a protective measure against increasingly sophisticated cyber threats and is crucial for maintaining secure access to sensitive resources.
As such, Defender for Identity is not just a solution for IT professionals but an important part of the security protocol for any organization that values the integrity and safety of its digital identity management. By implementing this advanced security measure, companies are better equipped to handle the evolving threats in today's digital environment.

People also ask
What is Microsoft Microsoft Defender for Identity?
Microsoft Defender for Identity is a cloud-based security solution that leverages on-premises Active Directory signals to identify, detect, and investigate advanced threats, compromised identities, and malicious insider actions directed at your organization. It's designed to help protect your enterprise from multiple types of advanced targeted cyber attacks and insider threats.
What should you do before you can use the Microsoft Defender for Identity Sensor?
Before you can use the Microsoft Defender for Identity Sensor, you need to prepare your environment. This involves validating your organization's prerequisites, which include ensuring the appropriate permissions, configuring the necessary Active Directory and network settings, and downloading the Defender for Identity Sensor. After the environmental prerequisites are met, you can install the Defender for Identity Sensor on your on-premises domain controllers to start monitoring and analyzing AD traffic for suspicious activities.
What are the roles in Defender for identity?
In Defender for Identity, there are various roles that determine levels of access and capability within the platform. Some of the key roles include: 1. **Defender for Identity Admins:** Have full access to the Defender for Identity portal and can manage all aspects of the service. 2. **Defender for Identity Users:** Can access the portal and conduct investigations, but they cannot manage the service. 3. **Defender for Identity Viewers:** Limited to accessing only the data and insights gleaned from the Defender for Identity service, without permissions to modify settings or configurations. 4. **Defender for Identity Security Readers:** Can receive and view security alerts, but they cannot alter any configurations or settings within the service. These roles help an organization to maintain a structured approach to security management and ensure that only authorized personnel take certain actions within Defender for Identity.
Which Microsoft 365 Defender solution can detect an Active Directory domain compromise?
The Microsoft 365 Defender solution capable of detecting an Active Directory domain compromise is Microsoft Defender for Identity. It specializes in identifying and investigating security threats on domain controllers, leveraging existing on-premises Active Directory signals to detect suspicious activities that may signify a domain compromise or other security breaches.
Keywords
Microsoft Defender for Identity Demo, Defender for Identity Tutorial, Learn Defender for Identity, Microsoft Security Training, Cybersecurity Identity Protection, Microsoft Identity Defender Guide, Identity Threat Detection Demo, Enterprise Identity Security, Microsoft Defender ATP Identity, Defender for Identity Skills.